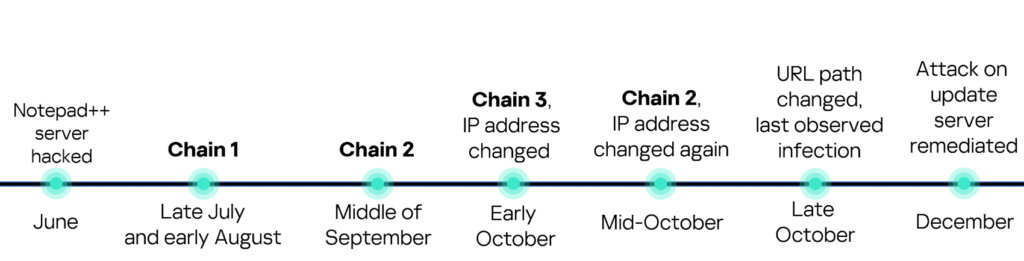
Security researchers have attributed the Notepad++ update hijacking to a Chinese government-linked espionage crew called Lotus Blossom (aka Lotus Panda, Billbug), which abused weaknesses in the update infrastructure to gain a foothold in high-value targets by delivering a newly identified backdoor dubbed Chrysalis.

The maintainer of Notepad++ has revealed that state-sponsored attackers hijacked the utility’s update mechanism to redirect update traffic to malicious servers instead.
“The attack involved [an] infrastructure-level compromise that allowed malicious actors to intercept and redirect update traffic destined for notepad-plus-plus.org,” developer Don Ho said. “The compromise occurred at the hosting provider level rather than through vulnerabilities in Notepad++ code itself.”
The exact mechanism through which this was realized is currently being investigated, Ho added.
The development comes a little over a month after Notepad++ released version 8.8.9 to address an issue that resulted in traffic from WinGUp, the Notepad++ updater, being “occasionally” redirected to malicious domains, resulting in the download of poisoned executables.
Early Monday, the text editor’s project author said a suspected Chinese state-sponsored group somehow compromised a shared hosting server and selectively redirected some update traffic to an attacker-controlled site where victims downloaded a poisoned version of what appeared to be a legit software update.
Later on Monday, Rapid7’s managed detection and response team attributed the attack “with moderate confidence” to the Chinese advanced persistent threat (APT) group they call Lotus Blossom.
This group typically conducts targeted cyber-espionage campaigns against organizations in Southeast Asia – and more recently Central America – with a focus on government, telecom, aviation, critical infrastructure, and media sectors.
According to the threat hunters, the espionage crew used the hijacked Notepad++ update to deliver a previously unknown backdoor called Chrysalis.
Notepad++ author Don Ho did not immediately respond to The Register‘s inquiries about Rapid7’s attribution and malware analysis. We will update this story if we hear back.
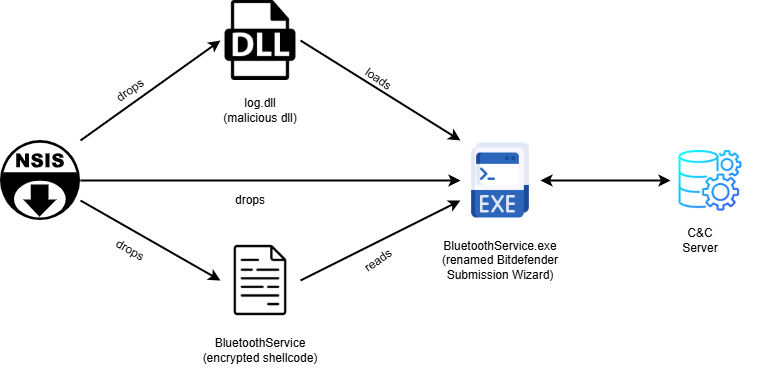
While it’s still unclear exactly how the miscreants gained initial access to Notepad++’s distribution infrastructure, once inside they abused that access to deliver a trojanized update in the form of an NSIS installer, a packaging format commonly abused by Chinese APT groups to deliver initial payloads.
The installer contained an executable file named “BluetoothService.exe,” which is a renamed legitimate Bitdefender Submission Wizard abused for DLL sideloading – another favorite technique among Beijing-backed spies to deliver custom implants. It also included a file called “BluetoothService” that is actually an encrypted shellcode, and a malicious DLL sideloaded by BluetoothService.exe.
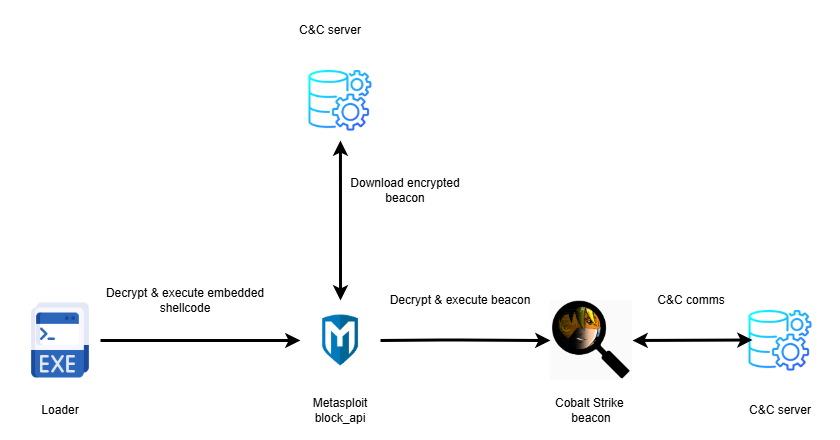
The shellcode here is the Chrysalis backdoor, and according to Rapid7, “its wide array of capabilities indicates it is a sophisticated and permanent tool, not a simple throwaway utility.”
It uses legitimate binaries to sideload a malicious DLL with a generic name to make sure it’s not discovered by simple filename-based detection tools. It also uses custom API hashing in both the loader and the main module, along with multiple layers of obfuscation to further cover its tracks, as well as “a fairly structured approach to C2 communication,” the researchers wrote.
As of press time, Rapid7 didn’t have visibility into how many victims inadvertently downloaded the Chrysalis malware – but we will update this story if we learn more. The security sleuths did, however, publish a full list of file and network indicators of compromise, so be sure to give that a read.
They note the attribution is primarily based on similarities between the initial loader use and previous research from Symantec, including the goon squad using a renamed Bitdefender Submission Wizard to sideload a file called “log.dll” for decrypting and executing an additional payload.
“In addition, similarities of the execution chain of ‘conf.c’ retrieved from the infected asset and other loaders that we found, supported by the same public key extracted from [Cobalt Strike] beacons delivered through ‘conf.c’ and ‘ConsoleApplication2.exe’ suggest with moderate confidence that the threat actor behind this campaign is likely Lotus Blossom,” the Rapid7 team wrote.
Myths vs Facts
Myth: Notepad++ khud insecure software hai
Fact: Issue software ka nahi, balki supply-chain compromise ka tha
Myth: Sirf China-based users affected hue
Fact: Attack global users ko target kar sakta tha
Myth: Sirf open-source tools hi vulnerable hote hain
Fact: Koi bhi popular software supply-chain attack ka shikar ho sakta hai
Myth: Antivirus sab kuch detect kar leta hai
Fact: Advanced backdoors jaise Chrysalis traditional AV ko bypass kar sakte hain
FAQs
#CyberSecurity #NotepadPlusPlus #ChrysalisBackdoor #LotusBlossom #Carrerbook #Anslation #ChineseHackers #APTThreat #MalwareAlert #SupplyChainAttack #TechSecurity #CyberEspionage
Discord Down: Messages Fail for Millions Worldwide
On 9 March 2026, the popular communication platform Discord experienced a major global outage that…
X (Twitter) App Dark Mode: Everything You Need to Know
Dark mode has become one of the most popular features in modern mobile applications, and…
Guardians of the Galaxy 85% OFF – Epic PS Deal!
Marvel’s Guardians of the Galaxy is now 85% off in the PS Store Dealmania sale….
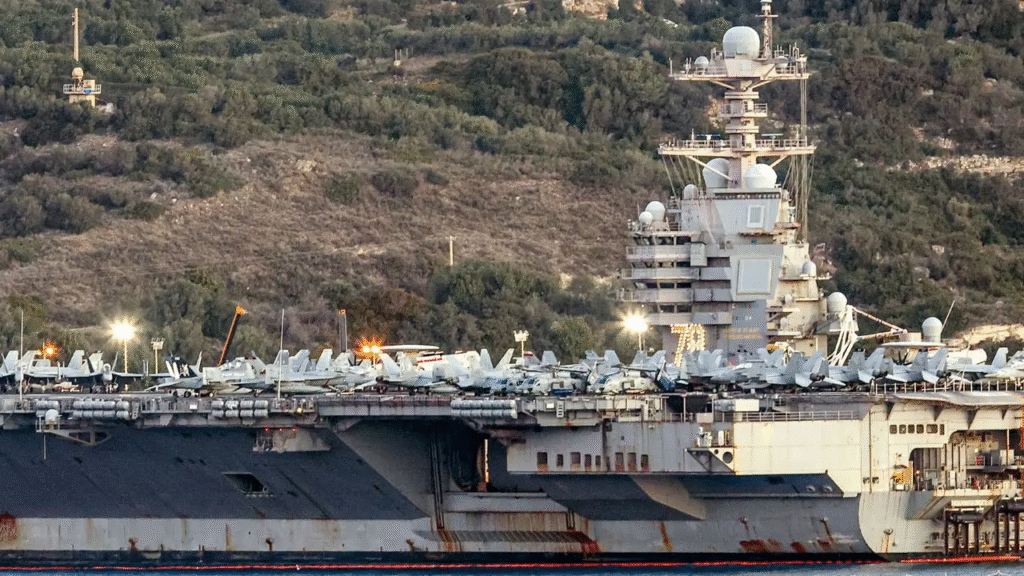
Iran’s New Chinese Missiles Could Shift Gulf Naval Balance
Rising tensions in the Middle East may be entering a new and more dangerous phase….
Massive YouTube Outage Hits 300K+ Users – Now Resolved
YouTube has confirmed that its services are fully operational again after a widespread disruption left…
powerful Xbox Services Down: Apps and Cloud Saves Disrupted
Xbox has officially confirmed a service disruption impacting certain console features, including streaming applications and…